- Mon 02 August 2010
- Cartographica
- Rick Jones
The violent tension between Palestine and Israel is no secret to those who watch the news on a regular basis. The violence often escalates into rocket attacks from Gaza that are known to strike civilian targets inside of Israel. Check out the latest NPR report discussing the damage cause by this morning's more recent rocket attack. In this post we will map several rockets commonly used by Palestinian militants to determine how far each rocket can strike.
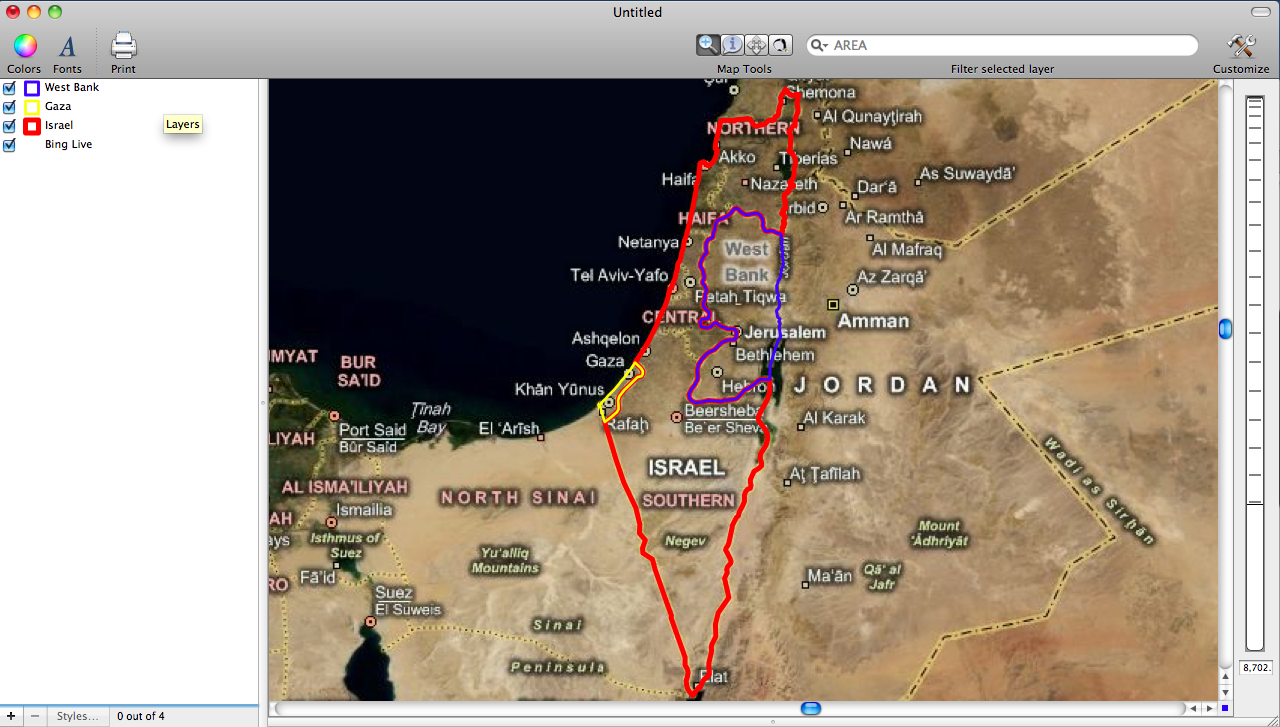
This post uses a combination of several different data sets. The base maps used in this example were collected at Doc Savage's website who is a Archaeologist that works in the region. In the first image you can see the political boundaries of Israel, Gaza, and West Bank, which are our regions of interest. I compiled and collected data on the types of rockets and the various ranges associated with each one.
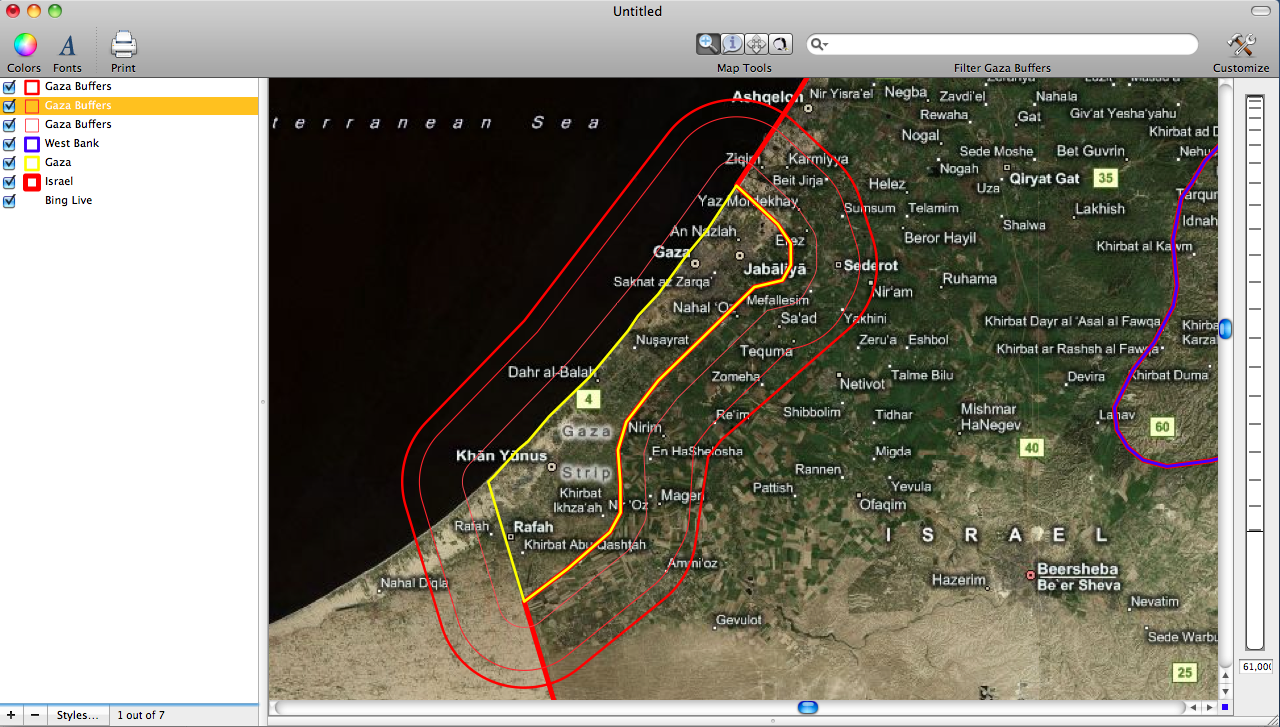
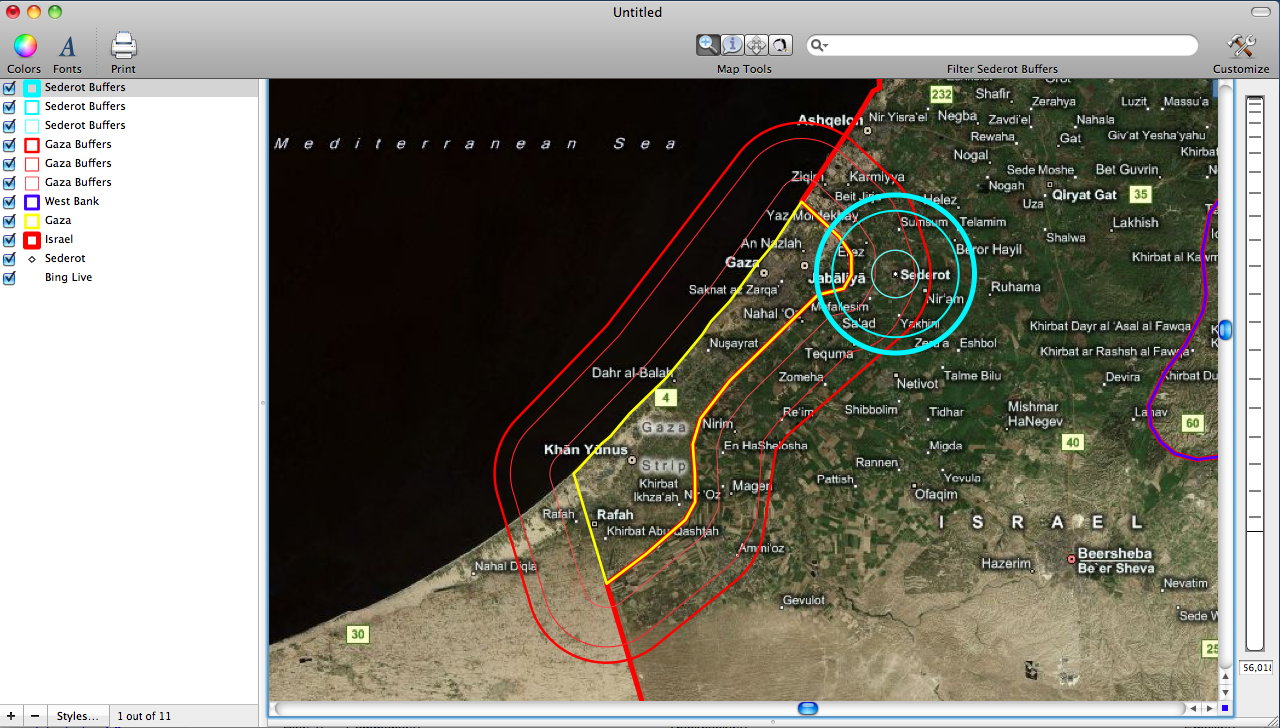
I am interested in the rockets fired into Israel from Gaza. In our analysis we need to look at two aspects of the rockets fired into Israel. First, we need to look at the type of rocket and its range. There is a nice overview of the rockets, called Qassam/Kassam rockets, on Wikipedia which describes how they are made and used. Based on the information on Wikipedia it appears that the rockets range from 3km to 10km in maximum range. The image below shows the areas in Israel at risk of being attacked by rockets.
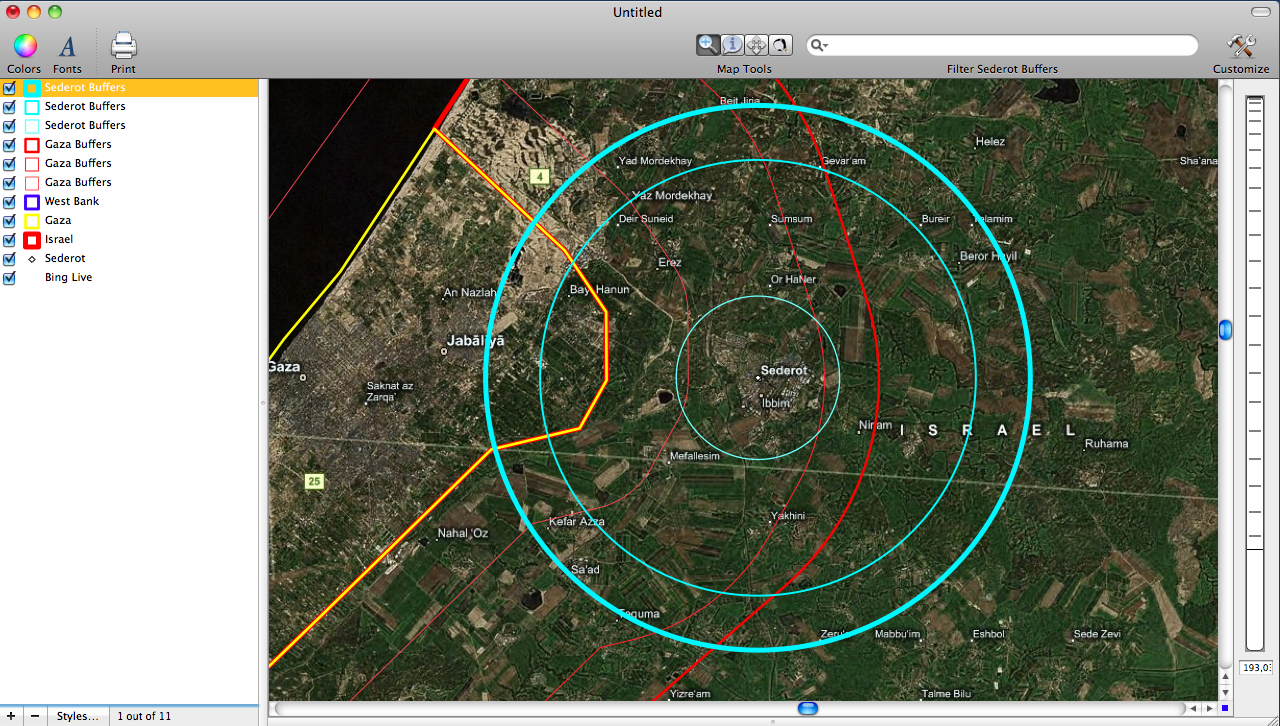
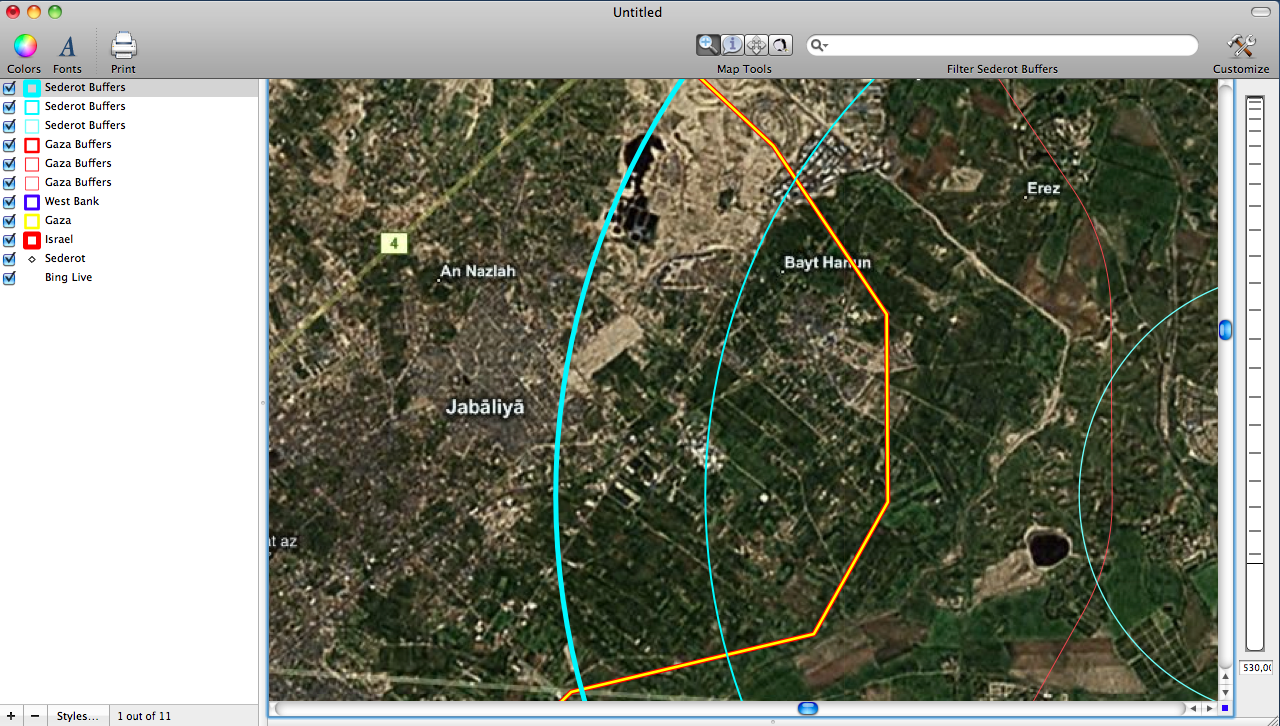
In most of my research on the rocket attacks it appears that most originate from Northern Gaza. Sederot is a Southern Israeli city that is regularly hit in rocket attacks, and it is located Northeast of Northern Gaza. We can use a process of creating buffers around Sederot to determine where it is most likely that attacks are originally launched. The third image shows the buffer around Sederot at 3km, 8km, and 10km. The areas where the Gaza border and the Buffers from Sederot intersect are the locations where attacks can be expected to come from when a rocket hits Sederot. The fourth image is a look at the areas identified as likely places where attacks originate from. Finally, the fifth image show the full extent of the situation with both sets of buffers shown.